What you can do
Ask a question. Get guidance, not just an answer.
Ask your regulations
Plain English in, cited answer out. The section number, the deadline, what to do about it.
Compare across markets
ERCOT vs PJM vs MISO vs NIS2. One question, every jurisdiction, citations to every section.
Know your obligations
Breach in Texas, operations in Frankfurt. Every reporting deadline, every authority, ranked by urgency.
How it works
Your sandbox. Your data. Nothing leaves.
Dedicated environment
Your own isolated sandbox. Your documents, your queries, your data. Nothing shared, nothing exposed.
Pick your sources
Select the regulators and frameworks that apply. ERCOT, NERC CIP, NIS2, FERC, or any combination.
Upload your documents
Compliance plans, policies, procedures. Update them anytime. Ask a question and both get searched together.
Ask anything
Get the answer, the section, the deadline, and what to do next.
Product
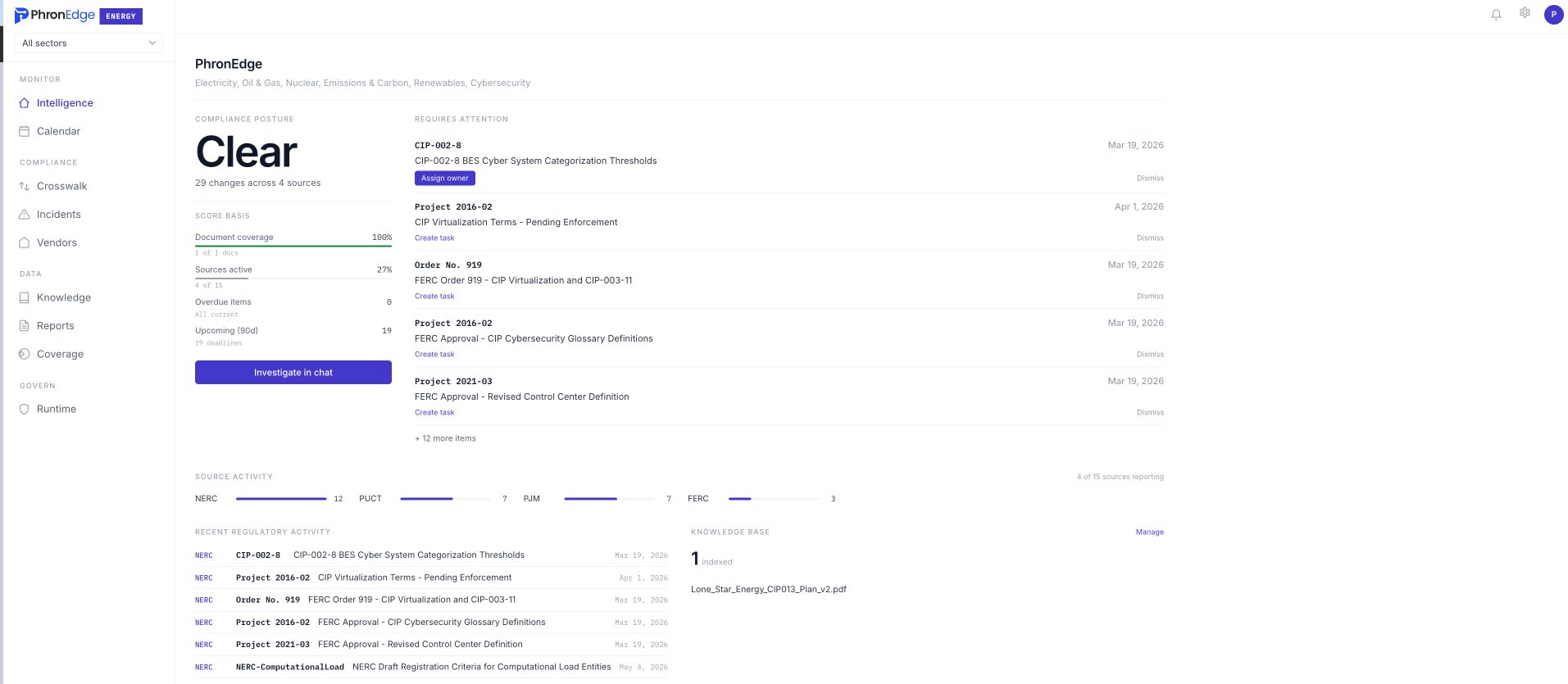
Your compliance posture. One screen.
Every applicable standard. Gaps ranked by risk. The evidence you need to close each one.
What we cover
Six sectors. Every regulation that governs them.
Every major wholesale electricity market covered. ERCOT, PJM, MISO, CAISO, ISO-NE, SPP, NYISO in the US. ENTSO-E in Europe. AESO and IESO in Canada. Ofgem in the UK. AEMO in Australia. Protocols run over 5,000 pages and update frequently.
"We spend $600K a year on three regulatory analysts reading the same protocol changes. Two weeks to produce a cross-market comparison that's already outdated by the time it reaches the VP."
GHG reporting, methane standards, carbon markets. EPA requirements tighten yearly. Missed reports trigger daily penalties.
"EPA amended the GHG rule. Does our Subpart W methodology still comply?"
NERC CIP, EU NIS2, UK NIS, AESCSF. Each defines different incident timelines, technical measures, and penalties.
"We operate in Texas AND Frankfurt. CIP-008 says 1 hour. NIS2 says 24 hours. Are we compliant?"
Solar, wind, battery storage. FERC Order 2023 is rewriting interconnection rules. IRA incentive compliance changes quarterly. PPA obligations span decades across multiple ISOs. Developers need cross-market intelligence to move fast.
"We have 14 projects in three ISO queues. FERC just changed the interconnection rules. Which of our applications are affected?"
Coverage
5 jurisdictions. 15 regulatory sources.
Why this matters
Read the rule yourself. Not someone's summary of it.
Cited to the section
Every answer links to the regulatory text. You verify it, not trust it.
See how citations workYour documents searched too
Upload compliance plans and policies. Ask a question and both get searched. Gaps show up on their own.
See the knowledge baseChanges caught in hours
Protocols revise frequently. Standards update quarterly. You find out the same day.
See the change feedFrom the field
We lost the first two weeks of every month figuring out what changed. Now we ask and get the answer with the source attached.
CIP-010 baseline deviation flagged. Instead of pulling three people off their work, one question got the answer with the exact section and a link to our own docs.
We operate in Texas and Frankfurt. Reconciling CIP-008 and NIS2 incident timelines was a spreadsheet. Now every obligation comes back ranked by deadline in one query.
Know what is coming before it arrives.
The next protocol revision drops this week. Your team should know before it matters.